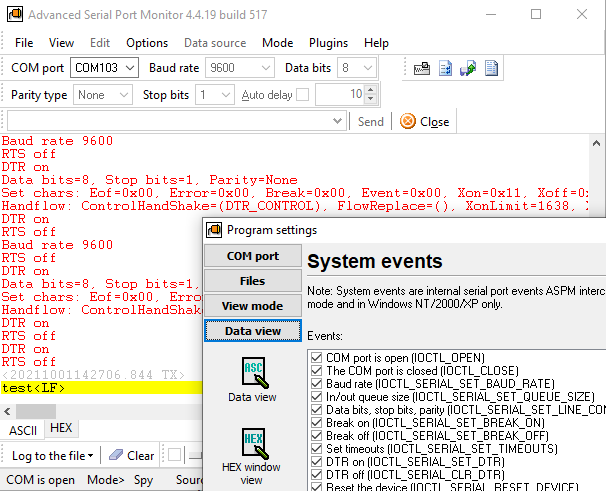
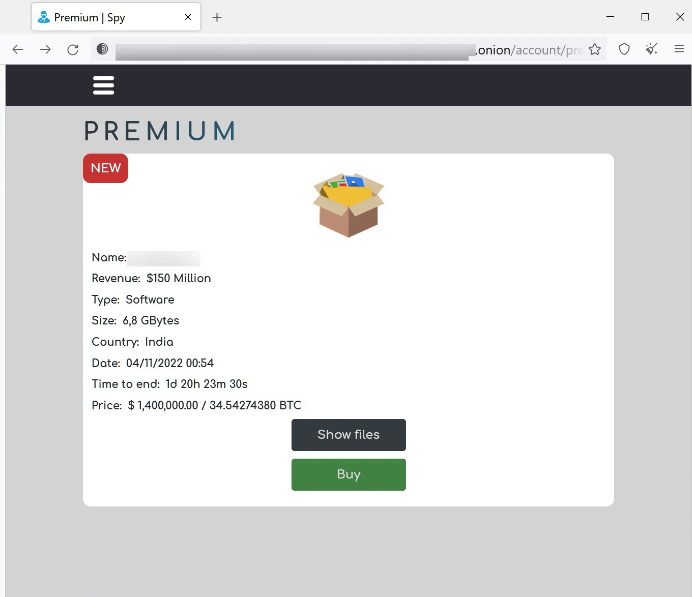
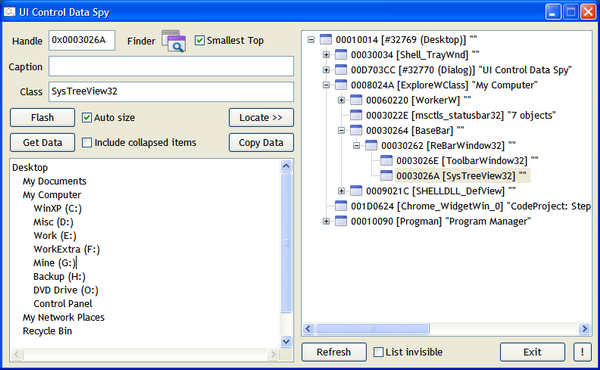
Industrial Spy ransomware uses double extortion attacks that combine data theft with file encryption - Industrial Cyber

Drones can be used to Spy on People and Gather Personal Data – 🌟 Wiperts: Reducing Identity Theft & Removing Personal Information Online

Digital Spy, Computer Data Safety In Cyberspace Stock Photo, Picture And Royalty Free Image. Image 46917770.

Hacker Spy Your Data File Stock Photo - Download Image Now - Binoculars, Network Security, Internet - iStock